What is Digital Signature?
Let's find in detail what is digital signature and how it can help you transform digitally.
#1
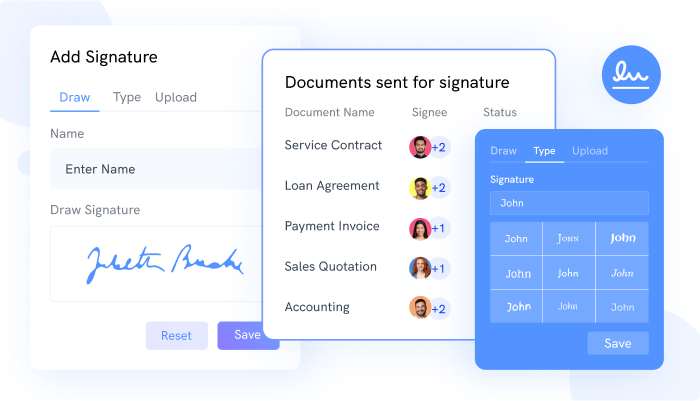
Get digital signatures on documents like sales contracts, employee HR letters, and more
#2
Create components like signature, date, initials on document via drag and drop builder
#3
Enable multi-party signing and share documents to multiple users
#4
Choose from 15+ scenario based pre-designed templates
#5
Upload documents from your local system or cloud providers like Dropbox, Google Drive and 500Box
#6
Track individual signee status for each document
#7
Send documents for signature from your favorite CRM software like CRM.io
#8
Set a hierarchical order for signing documents
#9
Unbelievable pricing - the lowest you will ever find
#10
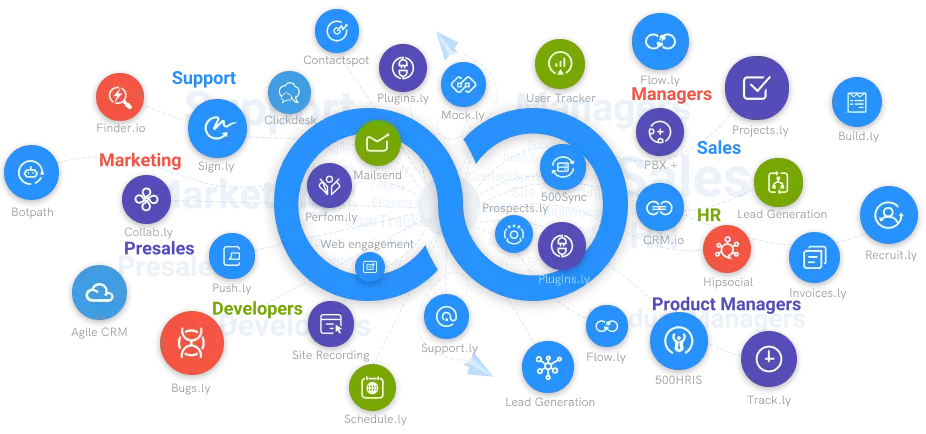
Everything your business needs - 50 apps, 24/5 support and 99.95% uptime
Overview
A digital signature is a sort of electronic signature (also known as an eSignature) that uses public-key cryptography to facilitate identity identification and data and transaction integrity. It's utilized to achieve the objective of delivering incontrovertible proof that a certain digital asset came from a specific person and hasn't been tampered with.
The authentication technique satisfies the need for the company to capture the signer's intent to sign. Several security functions are supported by digital signature creator. This technological profile, on the other hand, is focused on digital signatures, which are used to guarantee the integrity and validity of documents such as forms, agreements, and contracts, as well as to establish intent to sign.
Digital signatures are significant because they may assure message integrity from beginning to finish and offer authentication information about the communication's author. The digital signature online must be part of the application data and generated at the moment the message is created to be most effective. The signature is then double-checked when the message is received and processed.
You have the option of signing the entire message or sections of it (even overlapping parts of a message can be signed). If a portion of the message has to be changed before it reaches the customer, you can opt to sign just sections of it. If the entire message was signed in this circumstance, even if one element of the message was changed, the entire signature would be invalidated. You may create partial signatures for a message by adding a reference and an ID property to each element you want to sign.
When a signer electronically signs a document, the signature is produced with the signer's private key, which the signer always keeps safe. The mathematical method operates as a cipher, generating hashed data that matches the signed document and encrypting it. The encrypted data that results is used to create the digital signature. The time the paper was signed is also stamped on the signature. If the document changes after it has been signed, the digital signature becomes invalid.
"Certificates" are used in digital signing software. A certificate authority, or "CA", issues a secure personal key — a tool for encrypting a document – called a "digital signature certificate". The usage of digital certificates and public-key cryptography is made easier by a shared infrastructure known as public key infrastructure (PKI). Your certificate contains personal information such as your email address, name, address, and more.
Digital certificates:
You'll get both a private and public key (a "key pair") when you buy a digital signature certificate. At least one signer will provide their public key with the other party throughout the document approval process. If both parties are signing digitally, then both will share their private keys. A document's public key is used to decrypt it, but it cannot encrypt it in the first place.
Your certificate is kept on your computer's hard disc. You are the only one who has access to it. A digital certificate can also be saved on a customized USB stick.
Personal and Public Keys:
A hashed version of a document is produced whenever you sign it with your certificate. The text of the document is transferred using a hashing algorithm, which is a form of function that converts the original content into a digest of numbers and characters.
After that, your personal key is used to encrypt the digest. This is your “digital signature” — a protected version of the digest that can only be translated using your public key. It's important to note that the term signature does not just refer to a virtual signature](https://sign.cc/virtual-signature). It's a mix of the authorized document's content and your private key.
Matching the digest and the digital signature:
The digitally signed document is sent to the sender, who uses the public key to construct a hashed version of the original document and decrypts the recipient's digital signature to view the first hash value. The signature is verified if both of them match.
It's vital to remember this last point: if the content of the signed document was changed after it was signed, the hash in the digital signature will no longer match. A counterfeit signature, on the other hand, will not match the document's hash.
Sign.cc - Digital Signatures
Digital Signature companies, such as Sign.cc, make it simple to digitally sign documents using their solutions based on electronic signature technology. They offer a platform for transmitting and signing papers via the internet. Sign.cc is a free digital signature programme that allows you to digitally sign documents in PDF, Word, Excel, PowerPoint, and other formats with digital signatures for added security and protection.